Most engineers' first mental model of a proxy is essentially a smart router: traffic goes in, the source IP gets swapped, traffic comes out. That picture isn't entirely wrong — but it misses almost everything technically meaningful about what a proxy actually does. It leads to debugging the wrong layer when things break, and it doesn't explain why residential proxies behave differently from datacenter ones at the network level.
A proxy doesn't relabel packets. Depending on where it operates in the network stack, it terminates TCP connections, reads and reconstructs application-layer messages, modifies HTTP headers, and initiates entirely new network sessions on behalf of the client. Attributing TCP timeout behavior to application logic — or expecting header injection from a proxy that never touches L7 — means you're working with an incomplete model.
The sections below map exactly where proxies operate in the OSI stack, how traffic moves through each layer, and why a residential exit node produces a structurally different network fingerprint than a datacenter proxy.
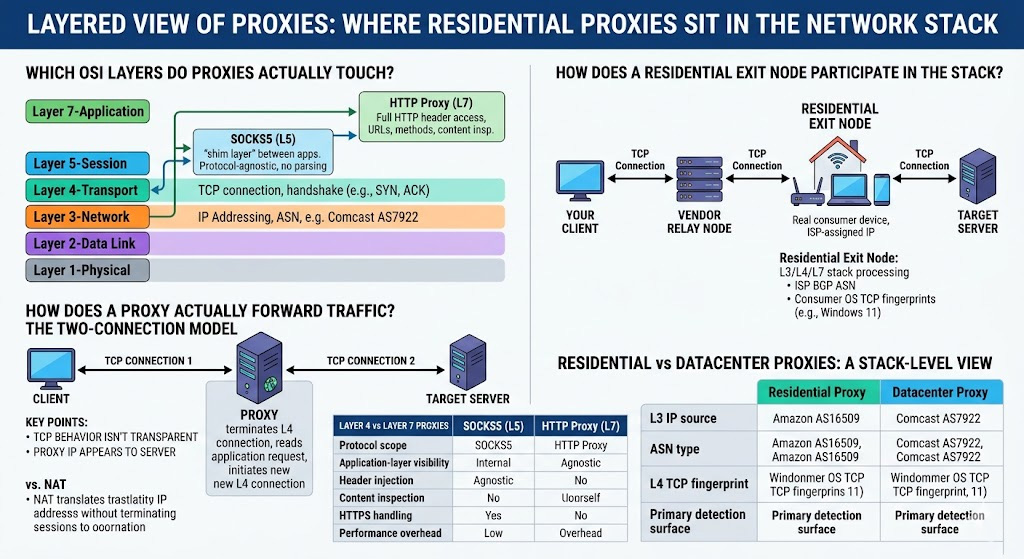
Which OSI Layers Do Proxies Actually Touch?
Proxies don't interact with all seven OSI layers equally. Four layers are relevant for practical proxy analysis:
| Layer | Name | Role in proxy traffic |
|---|---|---|
| L3 | Network | IP addressing and BGP routing — determines which ASN (and ISP or datacenter) an IP is attributed to |
| L4 | Transport | TCP connection establishment, handshake, teardown — where proxies terminate and re-establish sessions |
| L5 | Session | Where SOCKS5 operates: above TCP, below application-protocol parsing |
| L7 | Application | Where HTTP proxies operate: full access to HTTP headers, methods, URLs, and optionally payload |
L1, L2, and L6 don't participate in proxy forwarding logic and aren't relevant here.
One classification worth flagging upfront: the L5 position of SOCKS5 is standard industry shorthand, but RFC 1928 — the SOCKS5 specification itself — describes the protocol as "a shim-layer between the application layer and the transport layer." It doesn't sit cleanly at any single OSI layer. What matters practically is the behavioral distinction: SOCKS5 is protocol-agnostic and doesn't parse application-layer content, whereas an HTTP proxy does. That boundary drives every capability difference between the two.
How Does a Proxy Actually Forward Traffic? The Two-Connection Model
Here's what most proxy overview articles skip: a proxy doesn't forward packets. It terminates connections.
When a client connects through an L7 forward proxy, two separate and independent TCP connections exist simultaneously:
Client ──[TCP Connection 1]──► Proxy ──[TCP Connection 2]──► Target Server
↑
reads HTTP request at L7, re-originates
The proxy receives the client's TCP SYN, completes the three-way handshake, reads the incoming HTTP request at the application layer, then initiates a brand new TCP connection to the target server — its own SYN, its own sequence numbers, its own handshake. Cloudflare's proxy architecture documentation describes this directly: once a CONNECT tunnel is established, "there are two independent TCP connections; one on either side of the proxy." Maltz and Bhagwat's foundational work on TCP Splicing (IBM Research TR 21139, 1998) confirms the same two-connection structure from the performance angle — their throughput gains come precisely from optimizing the relay between these two independent sessions.
One place this becomes immediately practical: if you've ever seen a curl -v request hang at CONNECT while the same request succeeds without a proxy, the problem is almost always in Connection 2 — the proxy can't reach the target, or the target is refusing the proxy's IP. It's not a DNS resolution failure on the client side, and it's not a TLS issue. The hang point in the verbose output tells you which side of the connection is stuck.
Three implications of this two-connection model are worth internalizing:
TCP-level behavior isn't transparent. Retransmissions, window scaling, and congestion control on Connection 1 are independent from Connection 2. If you're debugging latency at the TCP level, the proxy is always a boundary, not a pass-through.
The proxy's IP appears in the L4 handshake with the server. The target never sees the client's IP in transport-layer headers — it sees whatever IP initiated Connection 2.
Error handling is decoupled. A timeout or reset on Connection 2 doesn't propagate to Connection 1 the way a routing failure would. This is why proxy-related timeout symptoms often look different from direct-connection timeouts.
This is the fundamental architectural difference between a proxy and NAT: NAT translates addresses at L3 without terminating sessions. A proxy terminates at L4, reconstructs at L7, and re-originates traffic from its own network stack — and the core of the two-connection model.
Layer 4 vs Layer 7 Proxies — What the Proxy Can See and Do
The protocol layer a proxy operates at directly determines its capabilities and constraints.
| Dimension | SOCKS5 (L5) | HTTP Proxy (L7) |
|---|---|---|
| Protocol scope | Any TCP or UDP traffic | HTTP and HTTPS only |
| Application-layer visibility | None — payload treated as opaque bytes | Full HTTP header read/write |
| Header injection | Not possible | Can add/modify X-Forwarded-For, Via, custom headers |
| Content inspection | Not possible | Possible for plaintext HTTP |
| HTTPS handling | Tunnels encrypted bytes transparently | Uses HTTP CONNECT to establish tunnel |
| Performance overhead | Lower (no L7 parsing) | Higher (HTTP message reconstruction) |
SOCKS5's protocol-agnostic nature makes it the only viable option for non-HTTP traffic — raw TCP applications, custom binary protocols, gaming traffic. An HTTP proxy simply won't handle it. Conversely, if you need header-level control — stripping or injecting X-Forwarded-For, managing cookies, modifying User-Agent before the request reaches the target — that work has to happen at L7. SOCKS5 can't touch it, and this isn't a limitation you can configure your way around. It's a consequence of which layer the protocol operates at.
How Does a Residential Exit Node Participate in the Stack?
Residential proxies become architecturally distinct here — not just commercially, but at the network-stack level.
A residential proxy service introduces a third actor: the exit node, a real consumer device (laptop, mobile phone, home gateway) running on an ISP-assigned connection. The full request path looks like this:
Your Client
│
▼ [TCP Connection 1 — L4/L7]
Vendor Relay Node (authenticates request, routes to exit node)
│
▼ [TCP Connection 2 — L4/L7]
Residential Exit Node (real device, ISP-assigned IP)
│
▼ [TCP Connection 3 — L4/L7] ← what the target server sees
Target Server
The exit node isn't forwarding a packet — it's a full network endpoint. Its operating system processes the complete L3-to-L7 stack:
L3: Packets leaving the exit node carry an IP address the ISP assigned via DHCP. That IP is registered in BGP routing tables under the ISP's ASN — not under a cloud provider or hosting ASN.
L4: The exit node's TCP stack performs its own three-way handshake with the target server. TCP fingerprinting tools like p0f will read the exit node's actual OS implementation — its window size, timestamp options, TTL. A Windows 11 home user on a cable connection produces a very different TCP fingerprint than a Linux server in a rack. From a bot detection perspective, this is a meaningful signal: a residential IP with datacenter TCP fingerprint characteristics (low initial TTL, uniform window size) can still get flagged even if the L3 address looks residential.
L7: The HTTP request is fully re-originated from the exit node. Depending on the exit node implementation, this may go through an embedded HTTP proxy on the device (in which case header injection is possible at that stage) or a SOCKS5 tunnel from a local browser instance (in which case you get a full browser fingerprint but no proxy-level header injection).
To judge which implementation your provider is using: check whether X-Forwarded-For headers appear by default in requests proxied through them. If they do, there's active L7 processing on the exit node side. If not, the traffic is being tunneled without application-layer intervention. Most providers document this in their API reference or will confirm it directly. The distinction matters because it determines whether header customization happens at the proxy configuration layer or has to happen in your automation framework.
Residential vs Datacenter Proxies: A Stack-Level View
Most comparisons between these two proxy types focus on block rates, speed, and pricing. The actual technical distinction lives at L3.
| Layer | Residential Proxy | Datacenter Proxy |
|---|---|---|
| L3 — IP source | ISP-assigned, DHCP, residential BGP prefix | Static, allocated to datacenter ASN |
| L3 — ASN type | Consumer ISP (e.g., Comcast AS7922, BT AS2856) | Hosting/cloud (e.g., Amazon AS16509, OVH AS16276) |
| L4 — TCP fingerprint | Real consumer OS — Windows, macOS, Android | Server-grade Linux, typically uniform per vendor |
| L7 — Header behavior | Depends on exit node implementation | Controlled by vendor infrastructure |
| Primary detection surface | Low at L3; manageable at L7 with proper config | High at L3 — ASN lookup flags as hosting |
Cloudflare's WAF and Bot Management platform explicitly expose ip.geoip.asnum as a rule condition, and their ASN list documentation directly describes using ASN lists to "manage traffic from ISPs and cloud providers where bots generating automated traffic might be hosted." Their bot management variables reference confirms that "checking ASN blocks" is part of their IP verification process. Akamai, PerimeterX, and similar platforms operate equivalent ASN-based scoring layers. An IP registered to a datacenter ASN is evaluated differently from one registered to a consumer ISP, regardless of how clean the L7 request looks.
That said, Cloudflare published a dedicated update to their residential proxy detection model in June 2024, specifically targeting residential proxy traffic that previously bypassed IP-based blocking. The L3 residential advantage is real, but it isn't a permanent free pass.
For legitimate use cases like ad verification and public data research, request consistency across layers matters beyond the IP origin alone. A request missing standard browser headers or with no cookie handling may be flagged as automated traffic regardless of where it originates — not because the IP is blocked, but because the request doesn't match the declared context. Ensuring your tooling produces requests consistent with its actual role (browser automation framework vs. API client) reduces the risk of compliant traffic being incorrectly challenged. The L3 BGP signal addresses one layer of evaluation; the rest depends on how well your implementation matches the traffic profile it's presenting.
What Can a Proxy See at Layer 7?
The answer depends entirely on whether the connection is plaintext HTTP or HTTPS.
Plaintext HTTP: An L7 forward proxy has full visibility. It reads the request line, all headers, and the body. It can modify, log, or reject any of this before forwarding. This is where X-Forwarded-For injection happens — the proxy appends the original client IP before passing the request downstream.
HTTPS via HTTP CONNECT: The client sends CONNECT target.example.com:443 HTTP/1.1 to the proxy. The proxy opens a TCP connection to the target and responds with 200 Connection Established. From this point, as RFC 7231 §4.3.6 specifies, the connection "is converted into a tunnel" — the proxy forwards encrypted bytes in both directions without being able to read them. No header injection, no content inspection, no modification past the CONNECT handshake.
For browser automation and web scraping — which is almost entirely HTTPS traffic in practice — the proxy's L7 role is limited to establishing that CONNECT tunnel. A common assumption is that the proxy handles User-Agent rotation or custom header injection automatically. For HTTPS traffic, it doesn't: those headers exist inside the TLS session, which the proxy can't see. Header rotation and user-agent configuration have to happen at the automation framework level, not in the proxy settings. In Playwright, that's page.setExtraHTTPHeaders(). In Scrapy, it's your downloader middleware. If you're seeing headers you expected the proxy to strip still appearing at the destination — or headers you configured in the proxy not showing up — this is the reason.
For cases requiring actual TLS-layer inspection (compliance logging, DLP enforcement), a terminating proxy with its own CA certificate is a different architecture entirely. The client has to explicitly trust that CA, and the proxy re-signs all certificates. That's out of scope for most scraping or automation use cases, but worth knowing the distinction exists.
Which Proxy Layer Does Your Use Case Need?
Three questions resolve most of the ambiguity quickly.
Does your traffic include non-HTTP protocols? If yes — raw TCP, SMTP, custom binary protocols, game traffic — SOCKS5 is your only option. HTTP proxies won't handle non-HTTP traffic by design.
Do you need HTTP header control at the proxy layer? If your use case involves injecting or stripping headers centrally (request signing, centralizing User-Agent logic), that requires L7. SOCKS5 can't touch L7 headers, full stop.
Is L3 IP reputation a factor? If the target platform performs ASN-based filtering — and most major web properties do — datacenter proxies carry a structural disadvantage at L3 regardless of L7 request quality. Residential proxies address this at the network layer.
For web scraping, browser automation, or ad verification against platforms running layered bot detection, residential proxies cover the widest range of the stack: authentic L3 BGP attribution combined with configurable L7 behavior. One real trade-off worth modeling before you commit: residential proxies are inherently slower than datacenter proxies. Real consumer devices on ISP connections carry higher and more variable latency than server hardware in data centers. If raw throughput is the priority and L3 IP trust isn't a constraint, that's a genuine cost.
Proxy001 operates a pool of 100M+ residential IPs across 200+ regions, with support for both HTTP and SOCKS5 protocol modes — so the layer choice is yours, not forced by the vendor's infrastructure. The IPs are ISP-assigned residential addresses, which means you get the L3 BGP attribution signal that datacenter proxies structurally can't replicate.
Next Steps
Residential proxies are a legitimate tool for ad verification, public data research, geo-targeted QA, and brand protection. Use cases involving access to systems or data without authorization fall outside these boundaries and may implicate the Computer Fraud and Abuse Act (US), the UK Computer Misuse Act, or equivalent statutes in other jurisdictions.
To observe the two-connection model directly, run curl -v --proxy http://your-proxy:port https://httpbin.org/ip — the verbose output shows the CONNECT handshake explicitly, making the L7 tunnel establishment visible as a discrete step. For deeper inspection, Wireshark on a loopback or tun interface capture will show independent TCP sequence numbers on each side of the proxy, confirming that the two connections are genuinely separate at L4.
For the underlying specifications:
RFC 1928 — the SOCKS5 protocol, including the "shim-layer" framing that clarifies its OSI position
RFC 7231, §4.3.6 — HTTP CONNECT method and tunneling semantics
Cloudflare's A Primer on Proxies — the two-connection model with HTTP/2 stream behavior included
Maltz & Bhagwat, TCP Splicing for Application Layer Proxy Performance, IBM TR 21139 (1998) — the foundational paper on two-connection relay architecture
Try Proxy001's Residential Proxies
If you're evaluating whether residential coverage produces a measurable difference for your use case — a scraper hitting ASN-filtering targets, geo-targeted content verification, or ad delivery testing across regions — Proxy001 offers a free proxy tier to test before committing. The network spans 100M+ real ISP-assigned IPs across 200+ regions, with native SDK support for Python, Node.js, Puppeteer, Selenium, and Scrapy. Both HTTP and SOCKS5 modes are available, so you can match the protocol layer to your actual infrastructure. The free tier is the fastest way to verify latency, compatibility, and whether the L3 BGP attribution change produces a measurable difference against your specific targets.











 English
English
 繁體中文
繁體中文
 Deutsch
Deutsch
 Français
Français
 Español
Español
 日本語
日本語
 Tiếng Việt
Tiếng Việt
 Português
Português