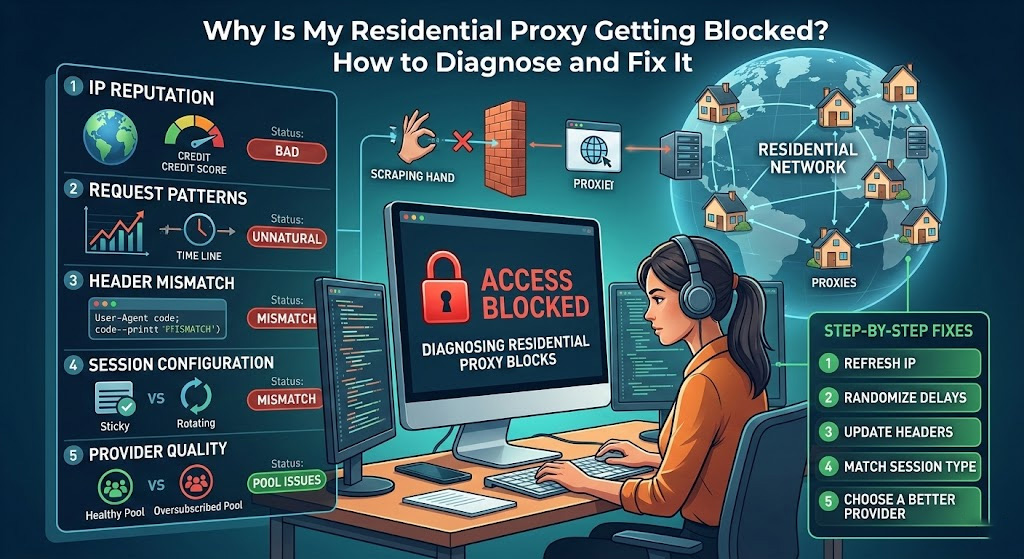
If Your Residential Proxy Is Getting Blocked, It's Usually One of These Five Things
Residential proxies are harder to detect than datacenter IPs—but they're not immune to blocks. When a residential IP gets flagged, it's almost always one of five root causes: a degraded IP, unnatural request behavior, misconfigured headers, a session setup mismatch, or a provider-side problem. This guide walks through each one with specific fixes.
Start by running this quick check: send a test request to ipinfo.io through your proxy. If the org field returns a cloud provider (AWS, Google Cloud, DigitalOcean) instead of a consumer ISP, stop here—your provider is delivering datacenter IPs labeled as residential. That's a provider problem, not a configuration problem.
If the IP checks out as genuinely residential, work through the causes below in order.
Cause 1: The IP Has a Poor Reputation
Not all residential IPs are equally clean. An IP that's been used heavily by multiple customers—or previously flagged by a target site—carries a degraded reputation score that bot-detection systems pick up even before your first request lands.
How to identify it:
Run your proxy IP through a reputation check tool such as Scamalytics or IPQualityScore. A risk score above 75 out of 100 means the IP is likely already on watchlists at major sites.
How to fix it:
Request a new IP from your provider. Reputable providers rotate degraded IPs out of their pools continuously—if yours doesn't offer replacements, that's a signal to reconsider the provider.
If you're on a rotating residential proxy network, increase your rotation frequency so you're less likely to land on a burned IP repeatedly.
Avoid reusing the same IP across multiple unrelated target domains. Each target site maintains its own blocklist, and cross-contamination is real.
Cause 2: Your Request Pattern Doesn't Look Human
This is the most common cause that users overlook. Even a genuinely residential IP will get blocked if the traffic coming through it looks nothing like a real person browsing. Modern bot-detection platforms—Cloudflare, Akamai Bot Manager, PerimeterX—don't just check the IP. They analyze behavioral signals: request timing, session length, interaction patterns, and idle time.[hydraproxy]
Real household traffic is irregular. It pauses, speeds up, hits dead ends, and varies. Automated traffic is clean, consistent, and perfectly timed—which is exactly what stands out.[reddit]
Patterns that trigger blocks:
Identical requests sent at fixed intervals (e.g., exactly every 2 seconds)
Sessions with no variation—no failed requests, no page-not-found responses, no idle periods
Hundreds of requests per minute from a single IP
Accessing only one URL type (e.g., only product pages, never homepages or category pages)
How to fix it:
Add randomized delays between requests—not a fixed 2-second pause, but a random interval between 1.5 and 4 seconds.
Vary your request patterns. If you're scraping product pages, occasionally request a category page or homepage in between.
Reduce concurrency. If you're sending 50 simultaneous requests through one IP, drop it to 3–5. Distribute higher volume across more IPs instead.
For rotating proxies, switch to per-request rotation rather than interval-based rotation when hitting rate-limited targets.
Cause 3: Your Headers Are Giving You Away
An IP address is only part of what a website sees. Every request also carries HTTP headers—User-Agent, Accept-Language, Accept-Encoding, Referer, and others. If your headers don't match what a real browser in your target region would send, the mismatch flags you as automated traffic regardless of how clean your IP is.[packetstream]
Common header mistakes:
Sending no User-Agent, or a default Python
requestsUser-Agent (python-requests/2.x.x)Using an English-language
Accept-Languageheader while targeting a non-English siteMissing standard browser headers that every real browser includes automatically
Sending a
Refererheader that doesn't match the navigation flow (e.g., jumping directly to a checkout page with no prior page visit in the referer chain)
How to fix it:
Use a realistic, up-to-date browser User-Agent. A current Chrome on Windows header looks like this:
pythonheaders = { "User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.0.0 Safari/537.36", "Accept-Language": "en-US,en;q=0.9", "Accept-Encoding": "gzip, deflate, br", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8", "Connection": "keep-alive"}Rotate your User-Agent strings across requests. Sending the exact same User-Agent on every request across thousands of sessions is itself a detectable pattern. Libraries like fake-useragent in Python make this straightforward.
Cause 4: Session Configuration Mismatch
Using the wrong session type for your task is a frequent cause of blocks that's easy to miss because everything looks configured correctly.
The core rule:
Tasks that require login or multi-step navigation → sticky sessions (same IP throughout)
Large-scale page scraping with no login → rotating sessions (new IP per request)
Mixing these up creates problems in both directions. If you're using rotating sessions on a site that requires login, the site sees a new IP on every request after authentication—a behavior no real user would exhibit, and a reliable trigger for session invalidation or an account lock.[joinmassive]
Conversely, if you're using sticky sessions for high-volume scraping, you're concentrating all your requests on one IP, accelerating the rate at which it hits per-IP thresholds.
How to fix it:
Audit your proxy client configuration. Confirm whether you're on rotating or sticky mode, and match it to your task.
For sticky sessions, check the session duration setting. Most providers default to 10 minutes—extend this if your workflow requires longer continuity, or shorten it if you're hitting rate limits.
If your provider's endpoint URL controls session type (common with username-parameter formats like
user-session-random123), verify the syntax in their documentation.
Cause 5: A Provider-Side Problem
Sometimes the issue isn't your configuration at all—it's the proxy pool itself. Oversubscription is a documented problem with lower-cost providers: too many customers routed through the same IP ranges, creating traffic density that no real residential network would produce.[hydraproxy]
Signs that the problem is provider-side rather than configuration-side:
You get blocked immediately on the first request, before any behavioral pattern could be established
The block is consistent across multiple IPs from the same provider on the same target
Testing the same request from your home IP works without issue[reddit]
Your IP reputation scores are consistently high across a large sample of IPs from the same provider
How to fix it:
Test a sample of 10–20 IPs from your provider against
ipinfo.ioand a reputation checker. If more than 30% score high-risk, the pool quality is the issue.Ask your provider directly about pool size, IP retirement policies, and oversubscription limits. Providers who can't answer these questions clearly are worth reconsidering.
For persistent issues, evaluate switching to a residential proxy service that actively monitors IP health and retires degraded addresses.
Quick Diagnostic Checklist
Run through this before changing anything in your code:
Does
ipinfo.ioconfirm a consumer ISP, not a datacenter, in theorgfield?Is the IP risk score below 75 on Scamalytics or IPQualityScore?
Are your request intervals randomized rather than fixed?
Is your User-Agent a current, realistic browser string?
Does your session type (rotating vs. sticky) match your use case?
Does the block happen on the first request, or only after several? (First-request blocks point to IP reputation; later blocks point to behavioral patterns)
Does the same request work from your home IP? (If yes, the proxy configuration is the issue. If no, it's a code or target-site issue)
Work through this list top to bottom. Most blocks resolve at step one, two, or five.
Compliance Note
The diagnostic steps above are for troubleshooting legitimate, authorized data collection workflows. If a target site's Terms of Service prohibit automated access, fixing your proxy configuration doesn't change that legal reality. Always confirm that your use case is permitted under the GDPR, CCPA, and the specific ToS of each target site before deploying any proxy-based workflow at scale.
Stop Troubleshooting Bad Infrastructure—Use Proxy001
Most proxy blocks come down to one thing: poor IP pool quality from a provider that doesn't actively manage IP health. Proxy001 maintains a residential proxy network built around clean, ISP-verified IPs with continuous health monitoring and automatic retirement of degraded addresses. With city-level geo-targeting, configurable rotating and sticky sessions, and infrastructure designed for legitimate business use cases—web scraping, ad verification, SEO research, and market intelligence—Proxy001 reduces the troubleshooting cycle that comes with low-quality proxy pools. Visit proxy001.com to explore plans and get started.











 English
English
 繁體中文
繁體中文
 Deutsch
Deutsch
 Français
Français
 Español
Español
 日本語
日本語
 한국어
한국어
 Português
Português