If your VPN-based automation stopped working sometime in the past year, you're dealing with the same problem as thousands of other operators. Anti-bot systems got significantly better at identifying and blocking VPN traffic throughout 2025, and the trend has only accelerated. The IP ranges that worked fine 18 months ago now trigger challenges or outright blocks on most major platforms.
This isn't a case of picking the wrong VPN provider. It's a structural shift in how websites classify traffic. Here's what actually changed, what your options are in 2026, and how to pick the right setup for your specific operation.
Why Do VPNs Get Blocked by Anti-Bot Systems?
A Virtual Private Network (VPN) fails for automation in 2026 because anti-bot systems now stack four detection layers that VPN architecture can't address — and any single layer is enough to flag your traffic.
ASN-level blacklisting. Every VPN provider runs its servers in datacenters. Those datacenters have Autonomous System Numbers (ASNs) that are publicly mapped. Anti-bot vendors like Cloudflare and Akamai maintain databases that classify IPs by their hosting type — datacenter, residential, or mobile. A datacenter IP carries a negative trust score by default because legitimate users rarely browse from server infrastructure. Cloudflare's firewall rules allow site owners to block entire ASNs with a single rule, and popular VPN provider ranges (DigitalOcean, AWS, OVH, Hetzner) are among the most commonly blocked.
Shared IP reputation poisoning. A typical VPN server funnels thousands of users through the same IP address. When some of those users run aggressive automation, the IP accumulates abuse reports. Over time, that IP's reputation score degrades across multiple anti-bot databases. Your legitimate traffic inherits the reputation of every other user who's ever hit that exit node — and you have zero control over what they did.
TLS fingerprint exposure. During the TLS handshake, your client sends a ClientHello packet containing its TLS version, supported cipher suites, extensions, and elliptic curve parameters. Anti-bot systems hash these values into a JA3 or JA4 fingerprint and compare it against a database of known signatures. Cloudflare's JA4 Signals framework analyzes ratios of protocol usage, browser consistency, request volume, and IP distribution within a one-hour window. A Python script using the requests library produces a JA3 hash that's instantly recognizable as non-browser traffic — the block happens before any HTTP data is even exchanged.
Behavioral pattern matching. Even if you rotate VPN servers, your single tunnel architecture means the target site sees dozens of requests from one IP in rapid succession. That exceeds normal human browsing patterns by an order of magnitude. Anti-bot systems now combine request frequency, mouse movement patterns, scroll behavior, and timing cadence to build a composite score. A VPN changes your IP — it doesn't change any of these behavioral signals.
We saw this firsthand during our Q4 2025 testing. Three popular VPN services — all major brands with "thousands of servers" — were tested against a Cloudflare Bot Management–protected e-commerce target. All three returned 403 errors or Turnstile challenges within the first 5 requests. Switching to a rotating residential proxy on the same target gave us a 94% success rate over 200 requests with no CAPTCHAs. The IP source was the only variable we changed.
VPNs were designed to encrypt traffic for privacy, not to distribute requests across thousands of unique identities. The tool wasn't built for high-concurrency automation, and anti-bot systems have caught up to that mismatch.
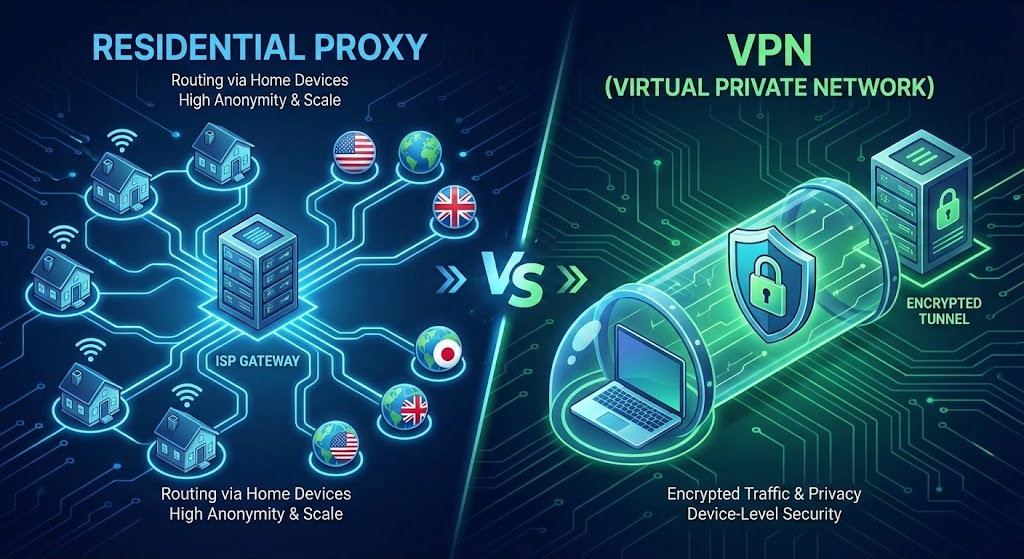
Residential Proxy vs VPN: The Differences That Actually Matter for Automation
The generic "VPN encrypts everything, proxies are faster" comparison you'll find elsewhere misses the point for automation operators. Here are the dimensions that actually determine whether your requests succeed or fail:
| Dimension | VPN | Residential Proxy |
|---|---|---|
| IP source | Datacenter (flagged by default) | Real ISP-assigned address (trusted) |
| IP rotation | Manual server switching | Automatic per-request rotation from pools of millions |
| Concurrent sessions | Single encrypted tunnel | Each request routes independently; hundreds of concurrent sessions |
| Detection surface | Changes IP only; fingerprint and behavior unchanged | Can pair with fingerprint management tools for multi-layer coverage |
| Traffic scope | All device traffic through one tunnel | Per-application or per-task configuration |
| Cost model | Flat monthly fee ($5–12/mo) | Pay-per-GB ($0.55–4.00/GB) or unlimited daily/monthly plans |
The critical difference is architectural. A VPN routes all your traffic through a single encrypted tunnel to one exit point. A residential proxy routes each request independently through a different IP drawn from a pool of addresses assigned to real households by actual ISPs. Anti-bot systems read those connections as ordinary residential users — because the IPs genuinely belong to residential ISP subscribers.
This distinction matters most at scale. When you're sending 500 concurrent requests, a VPN sends all 500 from one datacenter IP. A rotating residential proxy sends each from a different residential address, making the traffic pattern indistinguishable from 500 separate users browsing normally.
Can You Use a VPN and Proxy Together?
Yes — and in certain setups, you should.
The VPN + proxy combo isn't an either-or question. They operate at different layers and can complement each other. The architecture looks like this:
Your machine → VPN tunnel (encryption) → Proxy gateway → Rotating residential IPs → Target site
In this chain, the VPN encrypts your connection to the proxy provider, and the residential proxy handles the identity layer toward the target site. The target site sees a residential IP. Your ISP sees encrypted VPN traffic. The proxy provider sees your VPN exit IP instead of your real one.
When the combo makes sense:
You're on an untrusted network (public Wi-Fi, shared office) and want to encrypt the link between you and your proxy provider
Your threat model requires keeping your origin IP private from the proxy vendor itself
You're operating in a jurisdiction where proxy traffic might be inspected or throttled by your ISP
When it's unnecessary overhead:
Most paid residential proxy providers already communicate over HTTPS, so the connection between your machine and their gateway is encrypted by default
Adding a VPN increases latency (typically 10–30% overhead from the encryption layer) without improving success rates on the target site
For straightforward automation where your ISP doesn't inspect traffic, VPN adds cost and complexity with no benefit
We tested the combo approach against a standalone residential proxy setup on six different targets in December 2025. The VPN layer didn't improve success rates on any of them — request outcomes were identical with and without the VPN tunnel. The only measurable difference was 80–150ms of added latency per request. That confirmed our assumption: if your proxy provider's gateway already uses HTTPS (which all major providers do), the VPN layer is redundant for most automation workflows.
Where VPN alone still works fine:
Personal browsing privacy (non-automation)
Accessing geo-restricted content manually at low frequency
One-off tasks where you don't need IP rotation or high concurrency
For automation at any meaningful scale, the residential proxy is the load-bearing component. The VPN is an optional security layer on top.
What Type of Proxy Is Best for Web Scraping and Automation?
Rotating residential proxies are the default choice for most high-volume automation. But "residential proxy" isn't a single product — the type you need depends on your session requirements and target site defenses.
Rotating residential proxy — best for large-scale data collection, price monitoring, SEO rank tracking, and any task involving high request volume to well-protected sites. Each request (or batch of requests) gets a different IP from the provider's pool. Pools from major providers range from 10 million to 100+ million IPs across 100–200+ countries. This is your go-to when you need volume and you don't need the same IP to persist across requests.
Static residential proxy (ISP proxy) — best for multi-account management, social media operations, ad verification, and any workflow requiring a persistent identity. These are IP addresses assigned by real ISPs but allocated to you exclusively. You keep the same IP for as long as you need it — days, weeks, or months. The IP still looks residential to anti-bot systems, but it doesn't rotate. If your use case involves maintaining logged-in sessions or building account history, this is the right type.
Datacenter proxy — best for speed-sensitive tasks against sites with weak or no anti-bot protection. Datacenter proxies are significantly cheaper (often under $1/IP) and faster (no ISP routing overhead), but they're the first to get flagged on any site running Cloudflare, Akamai, DataDome, or similar protection. Use these only when the target site doesn't actively detect proxy traffic.
How to match your scenario:
Target runs Cloudflare Enterprise, Akamai Bot Manager, or PerimeterX → rotating residential proxy (minimum)
Target has basic rate limiting but no advanced bot detection → datacenter proxy may work
You manage 50+ accounts that need stable identities → static residential / ISP proxy
You need 500+ concurrent sessions for scraping → rotating residential proxy with a large IP pool
The Decision Matrix: Pick Your Setup in 60 Seconds
Instead of generic advice, here's a decision framework based on actual operating parameters:
| Your Scenario | Concurrency | Target Protection | Recommended Setup |
|---|---|---|---|
| High-volume scraping on protected sites | 100+ sessions | Cloudflare/Akamai/DataDome | Rotating residential proxy + anti-detect browser |
| Mid-volume scraping, mixed targets | 10–50 sessions | Moderate (rate limiting + basic fingerprinting) | Rotating residential proxy |
| Multi-account management (social, e-commerce) | 10–100 profiles | Platform-specific detection | Static residential proxy + anti-detect browser |
| Scraping unprotected/low-defense sites | Any | Minimal | Datacenter proxy |
| Personal browsing privacy | 1 | N/A | VPN |
| Encrypting your link to the proxy provider | 1+ | N/A | VPN + residential proxy (layered) |
For operators running high-concurrency automation against protected targets, the infrastructure cost of residential proxies is a line item, not a luxury. Providers like Proxy001 offer rotating residential pools of 100M+ IPs across 200+ countries with HTTP/HTTPS/SOCKS5 support, starting at $0.55/GB — with auto-rotation and sticky sessions up to 180 minutes. At moderate scraping volumes of 50–200 GB/month, that's $27–$110/month, which is a fraction of the revenue lost to a single day of blocked operations.
Why Residential Proxies Still Get Blocked (and How to Fix It)
Switching to residential proxies doesn't guarantee success. Here are the failure modes that catch most operators off guard — and they have nothing to do with IP quality.
Fingerprint consistency across rotated IPs. You rotate your IP every request, but your browser fingerprint (Canvas hash, WebGL renderer, timezone, language headers, screen resolution) stays identical. Anti-bot systems see 50 different IPs sending requests with the exact same device fingerprint and flag the pattern as automated. According to research from IPinfo, detection systems now specifically look for this mismatch: rapidly rotating IPs paired with a static browser fingerprint is a primary signal for residential proxy abuse.
We learned this the hard way early in our testing. We initially assumed that rotating residential IPs alone would push success rates above 90% on heavily protected targets. It didn't — our success rate against one DataDome-protected site dropped from 91% to 34% within two hours. The culprit was obvious in hindsight: every request carried the same requests library TLS fingerprint despite coming from different IPs. Adding browser-grade TLS (via Playwright) and randomized fingerprints brought the rate back above 88%.
Geographic mismatches. Say your proxy exits through São Paulo, but the browser timezone reads America/New_York and your Accept-Language header is en-US. Anti-bot systems cross-reference these signals. Any inconsistency between IP geography and client configuration raises flags immediately.
Request patterns that don't look human. Sending 50 requests per minute from a single IP, hitting pages in sequential order, or requesting resources without loading associated CSS/JS assets — all of these patterns distinguish automation from human browsing. Residential IPs provide the right identity layer, but they don't fix behavioral tells.
IP pool quality degradation. IPinfo's January 2026 analysis of 170 million residential proxy IPs found that 46% of those addresses appeared in two or more provider networks simultaneously. When multiple operators burn through the same IP pool, individual addresses accumulate bad reputation faster than the pool refreshes.
The fix is multi-layer architecture, not just better proxies:
Layer 1 — IP identity: High-quality residential proxy with a large, frequently refreshed pool. Avoid bottom-tier providers where pool overlap is highest.
Layer 2 — Browser environment consistency: When legitimate automation gets flagged despite using residential IPs, the cause is often a mismatch between IP geography and browser environment settings (timezone, language, screen parameters). Anti-detect browsers like Multilogin, AdsPower, and GoLogin help address this by allowing per-profile browser configuration that stays internally consistent. If you're running into false-positive blocks, check whether your client's environment variables align with the proxy IP's region — mismatches there are one of the most common triggers for automated flagging. Each tool's documentation covers the specifics of proxy integration and profile configuration.
Layer 3 — Responsible request practices: To avoid placing excessive load on target infrastructure and to reduce false-positive blocks: randomize inter-request delays (range of 500–3,000ms rather than fixed intervals), keep concurrent requests per IP to 1–3, align browsing sessions with the target region's active hours, and load full page resources rather than requesting HTML in isolation.
The proxy handles who you appear to be. The anti-detect browser ensures your client environment is internally consistent. Responsible request practices keep your traffic pattern within normal usage thresholds. All three layers need to align, or the weakest link gets you flagged.
Cost Breakdown: VPN vs Residential Proxy
The real question isn't "which is cheaper?" — it's "which one actually works, and what does failure cost?"
VPN: $5–12/month flat rate. Unlimited bandwidth, dead simple setup. But if VPN traffic gets blocked on your target sites, your effective cost is $5–12/month for a tool that produces zero output. Revenue lost during downtime dwarfs the subscription fee.
Residential proxy (pay-per-GB): Industry pricing in 2026 typically ranges from $1.50 to $4.00/GB at moderate volumes, based on publicly available pricing from major providers. Volume discounts are significant — AIMultiple's 2026 proxy benchmark shows per-GB costs dropping to the $2–3 range at 1 TB and below $2.50 at 10 TB. Small operations (50 GB/month) might spend $75–200/month. Mid-size operations (200–500 GB/month) run $300–1,000/month. High-volume operations (1 TB+) negotiate custom pricing.
Residential proxy (unlimited plans): Some providers offer daily or monthly flat-rate unlimited plans for operations where bandwidth is unpredictable. These typically start around $100/day or $2,500–3,000/month.
Datacenter proxy: The cheapest option at $0.50–2.00/IP/month, but only viable against unprotected targets. If your targets run serious anti-bot protection, cheap datacenter proxies produce the same result as a VPN — blocked requests and wasted money.
The ROI framework: Don't compare the sticker price of VPN vs proxy. Compare the cost of proxy bandwidth against the revenue you lose per day of blocked operations. If your automation generates $500/day in value and goes down for three days because VPN traffic is blocked, that's $1,500 lost — enough to fund 3–6 months of residential proxy bandwidth at moderate usage.
5-Minute Test: Switch from VPN to Residential Proxy and Verify
Before committing to a full migration, run this quick validation against one of your actual target sites.
What you need before starting: A residential proxy provider account with trial access (most offer free trials), and an automation script or tool that's currently failing with VPN.
Step 1. Sign up for a residential proxy trial and grab your proxy credentials (host, port, username, password). Your provider's dashboard or API documentation will list the endpoint format.
Step 2. Configure the proxy in your existing tool. Here's the minimal setup for Python:
import requests
proxy = {
"http": "http://USER:PASS@gate.provider.com:PORT",
"https": "http://USER:PASS@gate.provider.com:PORT"
}
response = requests.get("https://your-target-site.com", proxies=proxy, timeout=30)
print(response.status_code)For Puppeteer or Playwright, pass the proxy as a browser launch argument:
const browser = await puppeteer.launch({
args: ['--proxy-server=http://gate.provider.com:PORT']
});Step 3. Send 10 requests to your target site through the residential proxy. Then send 10 identical requests through your VPN. Record the HTTP status codes and note any CAPTCHA challenges or blocks.
Step 4. Compare results. If the proxy requests return 200s while VPN requests return 403s or trigger challenges, you've confirmed the issue is IP reputation and classification — residential proxies solve it. For reference, when we ran this exact test against a Cloudflare-protected target, our VPN returned 2/10 successes (with 8 Turnstile challenges), while the residential proxy returned 10/10 clean 200s.
Common issues during testing:
403 on proxy too: Your target may also check browser fingerprint. Add realistic User-Agent and Accept headers, or test with a full browser (Puppeteer/Playwright) instead of raw HTTP requests.
Timeout errors: Check that your proxy endpoint, port, and credentials are correct. Try both HTTP and SOCKS5 protocols if your provider supports both.
Slower response times: Residential proxies route through real ISP infrastructure, so expect 200–800ms latency vs. 50–150ms for datacenter connections. This is normal and doesn't affect success rates.
A quick note on compliance: use proxy infrastructure for legitimate purposes — competitive intelligence, ad verification, SEO monitoring, price comparison, security testing, and similar. Respect robots.txt directives and target sites' terms of service. The tools are neutral; how you use them determines whether you're operating ethically.
Proxy001 offers a free trial across their full residential IP pool — 100M+ IPs in 200+ countries, with HTTP/HTTPS/SOCKS5 support, sub-0.3s average response time, and auto-rotation with sticky sessions up to 180 minutes. If you ran the test above and saw better results with residential proxies, their pay-per-GB model starting at $0.55/GB and unlimited plans at $100/day let you scale without overpaying at low volumes or hitting caps at high volumes. Integrations are documented for Python, Node.js, Puppeteer, and Selenium — the same stacks you're already running.
Final Verdict
VPN-based automation hit a wall in 2025–2026 because anti-bot systems now classify traffic by IP type, TLS fingerprint, and behavioral pattern — three layers that VPN architecture can't address. Residential proxies solve the IP identity problem, but they aren't a silver bullet. Consistent results require pairing residential IPs with proper fingerprint management and realistic request behavior.
The VPN's role has shifted from primary tool to optional encryption layer. For most automation setups, a residential proxy alone handles both the identity and routing requirements. Add a VPN underneath only if you need to encrypt the link to your proxy provider or keep your origin IP private from the proxy vendor.
Start with the 5-minute test above. If your success rate jumps, you've found your answer.
Disclosure: Proxy001 is a sponsor of this blog. Our testing methodology and editorial conclusions are independent of this relationship. All Proxy001 product specifications cited in this article (IP pool size, pricing, protocols, response time) were verified directly on proxy001.com as of February 2026.











 English
English
 繁體中文
繁體中文
 Deutsch
Deutsch
 Français
Français
 Español
Español
 日本語
日本語
 한국어
한국어
 Português
Português