In a compliance review we ran with an enterprise data team last quarter, their DPO flagged residential proxies as an unresolved audit item. The proxies had been running in production for six months. Nobody had signed a DPA with the provider. Nobody had documented a lawful basis for the data collected. The provider's site said "GDPR compliant"—and the team assumed that covered them.
It doesn't. That assumption is the single most common compliance gap we see in organizations that use residential proxies for data collection, ad verification, or price monitoring.
Residential proxies are legal tools. But "it's legal" is the floor, not the ceiling. The actual question your compliance team is asking is: what specific obligations does your organization carry when it deploys a residential proxy network, and how do you document and execute each one?
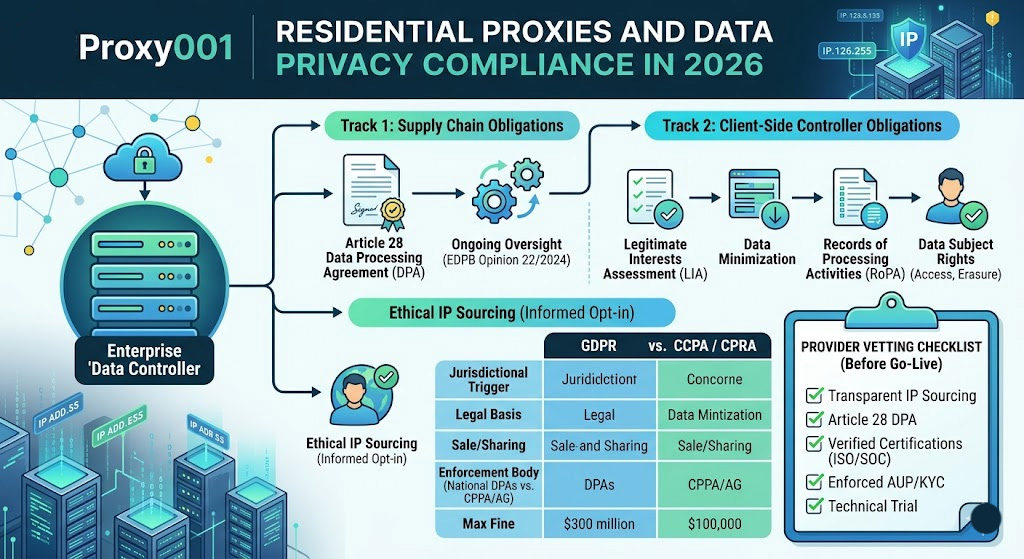
What follows maps every compliance layer—including the two separate tracks most teams miss, how GDPR and CCPA diverge for proxy users, and a concrete provider vetting process you can run before go-live.
Do Residential IP Addresses Count as Personal Data Under GDPR?
The answer isn't a flat yes or no—it depends on context, and the EU framework is deliberately broad.
GDPR Recital 30 states that online identifiers like IP addresses "may be used to create profiles of the natural persons and identify them." The operative word is may—GDPR doesn't require that identification actually occurs; it requires that identification be possible with reasonable effort. The EDPB reinforced this in its 2022 ruling on the IAB Europe Transparency & Consent Framework, confirming that IP addresses combined with behavioral signals routinely qualify as personal data.
The practical implication for residential proxy users: residential IPs are assigned by ISPs to real households. Unlike data center IPs registered to commercial entities, residential IPs trace back to identifiable individuals in ISP subscriber databases. Any server you query receives and can log that IP. If you're retaining those logs, or if a target site combines that IP with cookies, session data, or browsing behavior, you're processing personal data—full stop.
This is where the compliance distinction between ISP proxies and residential proxies becomes meaningful. ISP proxies (data center IPs registered under ISP blocks, sometimes called static residential proxies) sit further from individual identification than true residential proxies, since they're not assigned to specific households. That's not a reason to skip compliance analysis, but it's a relevant difference in risk profile when you're completing your Legitimate Interests Assessment. If you're routing through real residential nodes, treat the IPs as personal data by default—that's how the EDPB expects you to reason.
Which GDPR Lawful Basis Applies to Your Proxy Use Case?
Before your organization processes any personal data—including residential IPs—you need a documented lawful basis under Article 6. There are six; for most commercial proxy use cases, only one is realistic.
Consent (Art. 6(1)(a)) is clean in theory, unworkable in practice. You'd need prior, specific, informed consent from every individual whose data you process—impossible when you're collecting data from third-party sites via proxy.
Legitimate Interests (Art. 6(1)(f)) is the applicable basis for most commercial scraping and proxy-based data collection. The EDPB published Guidelines 1/2024 on legitimate interests in October 2024, which codifies a three-step test you must document before processing:
Purpose test: Is there a real, lawful legitimate interest? (e.g., competitive price monitoring, fraud detection, ad verification)
Necessity test: Is processing personal data actually required to achieve that purpose, or would a less intrusive method work?
Balancing test: Do your interests outweigh the data subjects' fundamental rights in this specific context?
This analysis must live in a Legitimate Interests Assessment (LIA) document—completed before any processing begins. France's CNIL issued specific guidance on web scraping and legitimate interests in January 2026, noting that large-scale automated data collection "can have major impacts on data subjects" and that this weighs against the controller in the balancing test unless adequate safeguards are documented.
Here's how common use cases map to GDPR requirements:
If your use case falls in the "contested" or "no lawful basis" rows, stop before you start. Consult your DPO and external counsel before any live deployment—enforcement actions in these categories are documented, and "we didn't know" doesn't hold up well.
One broader point worth flagging: the HiQ v. LinkedIn litigation shows why "public data" isn't a compliance blanket. The Ninth Circuit ruled in April 2022 that scraping publicly accessible data doesn't violate the CFAA. But a California district court separately found in November 2022 that hiQ breached LinkedIn's User Agreement—a distinct legal exposure. GDPR, ToS law, and computer fraud statutes run on parallel tracks. Clearing one doesn't clear the others.
Why "Choosing a Compliant Provider" Is Not Enough
This is the most commonly misunderstood point in the residential proxy compliance space, and it's where the real audit exposure lives.
The assumption most teams operate under: If we pick a GDPR-compliant proxy provider, we're covered. That logic is incomplete because your compliance obligations run on two independent tracks.
Track 1 — Supply Chain: What You Owe the Provider Relationship
Your proxy provider acts as a data processor under GDPR Article 28 when its infrastructure carries personal data on your behalf. As the data controller, that creates three concrete obligations.
First, sign a Data Processing Agreement (DPA) before any processing begins. (Note: "DPA" here refers to a Data Processing Agreement—a controller-processor contract required under Article 28. The same abbreviation is also used for Data Protection Authority, i.e., a national supervisory body; the two are distinct and both appear later in this article.) Under Article 28(3), the DPA must specify: the subject matter and duration of processing, the nature and purpose, the types of personal data and categories of data subjects, the rights and obligations of each party, sub-processor authorization terms, and deletion or return provisions at contract end. A standard terms-of-service document does not substitute for this.
Second, treat the DPA as a living obligation—not a one-time checkbox. The EDPB's Opinion 22/2024, published October 7, 2024, confirms that the obligation to verify processor compliance is continuous—"the controller should, at appropriate intervals, verify the processor's guarantees." It also extends this obligation down the sub-processor chain: you're responsible for ensuring your provider has passed the same obligations to any infrastructure layers beneath them.
Third, account for IP sourcing in your risk assessment. If your proxy provider enrolled residential nodes through hidden SDK injection, traffic hijacking, or botnet-adjacent methods, you're the downstream beneficiary of that infrastructure. In January 2026, Google's Threat Intelligence team disrupted IPIDEA—at the time the world's largest residential proxy network—specifically because it embedded undisclosed proxy functionality in software users installed unknowingly. The "I didn't know how the IPs were sourced" defense carries very little weight in this regulatory climate.
Practically, this means your due-diligence record on IP sourcing needs to be documented before you sign any contract—a completed supplier questionnaire, a written statement from the provider on their opt-in consent model, or a Vendor Risk Assessment that explicitly covers node acquisition methods. Ethical IP sourcing means node owners gave explicit, informed opt-in consent and can withdraw it at any time.
Track 2 — Client Side: Your Own Data Controller Obligations
Even if your provider's infrastructure is fully compliant, everything you collect, store, and process afterward is your own GDPR responsibility. Your LIA covers collection. But you also need:
Data minimization (Art. 5(1)(c)): Retain only what's necessary for the documented purpose. Price monitoring needs price data—not session IDs, browsing patterns, or incidental signals.
Storage limitation (Art. 5(1)(e)): Set and enforce a specific retention period. "We'll delete it when it's no longer needed" isn't a policy.
Data subject rights (Arts. 17–21): If an individual requests erasure of their data—including IPs you logged during a scraping run—you have 30 days to respond.
Records of processing activities (Art. 30): Your proxy-based data collection must appear in your RoPA. This is typically the first document a regulator requests.
Common Compliance Misconceptions
GDPR vs. CCPA: Where the Compliance Rules Diverge for Proxy Users
If your proxy-based data collection touches both EU residents and California consumers, you're dealing with two separate compliance tracks that share vocabulary but not obligations. Here's where they diverge specifically for proxy users.
The CCPA "sharing" exposure: Under CPRA (effective since January 2023), sharing personal information for cross-context behavioral advertising—even without direct monetary exchange—requires providing consumers an opt-out mechanism. If you're using residential proxies to collect consumer behavior data and passing it to any analytics or advertising platform, you may have created a "sharing" relationship under California law. The CPPA announced a joint investigative sweep in September 2025 (see cppa.ca.gov/announcements/2025/20250909.html) specifically targeting businesses failing to honor opt-out signals for the sale and sharing of personal data—and new CCPA regulations effective January 1, 2026 expand obligations around cookie consent, GPC signals, and privacy policies.
The CCPA service provider agreement is not the same as a GDPR DPA—but it's equally non-optional. Under CPRA §1798.140(ag), a written service provider contract must, at minimum: prohibit the provider from retaining, using, or disclosing your data for any commercial purpose outside the stated service; prohibit combining your data with data obtained from other sources for the provider's independent purposes; and include a downstream prohibition on selling or sharing that data. Unlike a GDPR DPA, there's no single mandated format, but those three prohibitions must be explicit in the contract language.
Beyond GDPR and CCPA: Brazil's LGPD, Thailand's PDPA, and India's Digital Personal Data Protection Act 2023 follow broadly similar logic—automated collection of personal data requires either a lawful basis or consent, and cross-border transfers need additional safeguards. Building your program to GDPR standards first is the most defensible baseline, since it's the strictest framework with the deepest enforcement record.
How to Vet a Residential Proxy Provider for GDPR/CCPA Compliance
This is where analysis becomes action. The following process covers what you actually need to verify before signing with any provider.
Before you start, make sure you have:
Your use case documented (what data you're collecting, why, for how long)
Clarity on which regulations apply to your organization
Your DPO or legal counsel briefed on the evaluation scope
Step 1: Confirm IP sourcing transparency
Ask the provider directly how residential IPs are enrolled in their network. A legitimate provider can document its opt-in consent flow—showing, for example, that users who install an SDK explicitly agreed in clear language that their device will function as a proxy exit node, and that they can withdraw that consent at any time. If a provider deflects this question, refers you to marketing materials, or says sourcing methodology is proprietary, treat it as a material risk. We've seen this question catch providers off guard—which itself is informative. After the January 2026 IPIDEA takedown, "opaque sourcing" is no longer a theoretical compliance concern; it's a concrete infrastructure liability.
Step 2: Obtain and review the DPA
Request the provider's Data Processing Agreement before any trial or purchase. Check it against Article 28(3): Does it define the processing subject matter, duration, and purpose? Does it list sub-processors and include a change-notification clause? Does it contain a deletion/return provision at contract termination? If the provider offers only a ToS or says the ToS is sufficient, that's noncompliant under GDPR—full stop. Pay attention to the sub-processor list. Large residential proxy networks route traffic through multiple infrastructure layers, and per EDPB Opinion 22/2024, you have both the right to know who handles your data and the obligation to verify it.
Step 3: Verify third-party certifications independently
ISO/IEC 27001:2022 certification is the baseline expectation. Ask for the certificate number and verify it through the issuing accreditation body—UKAS (UK), DAkkS (Germany), ANAB (US), and similar bodies publish searchable online registries. SOC 2 Type II reports are a stronger signal than Type I, since they cover a 6–12 month operational period rather than a single point-in-time audit. If a provider claims certifications but can't produce verifiable documentation, that's a compliance red flag regardless of how their residential proxies pricing compares to competitors.
Step 4: Evaluate KYC and AUP enforcement
Providers that don't scrutinize customer use cases are an increasing liability—for themselves and for their customers. Ask whether the provider conducts use-case review during onboarding. An acceptable use policy prohibiting illegal scraping, credential stuffing, and fraud is table stakes; what matters is whether there's evidence it's enforced. Some enterprise providers have begun requiring customers to document their scraping use cases. That's not a burden—it's actually a positive compliance signal.
Step 5: Run a technical trial before committing
Compliance review and technical validation should happen in parallel. Proxy001 offers a free trial—no credit card required—that lets you test its residential proxy network across 100M+ IPs in 200+ regions against your actual infrastructure before any commercial decision. Use the trial to verify latency, geo-targeting accuracy, and success rates on your target domains. Use the same window to request Data Processing Agreement documentation and confirm compliance materials with the Proxy001 team.
Verification checklist before go-live:
✅ Written confirmation of opt-in IP sourcing model, with documentation available
✅ Executed Data Processing Agreement (DPA) covering all Article 28(3) requirements
✅ ISO 27001 certificate number verified through accreditation body registry
✅ Sub-processor list obtained and reviewed
✅ AUP reviewed and confirmed to prohibit illegal uses
Troubleshooting common vetting issues:
Provider says their ToS covers GDPR compliance. A ToS governs the commercial relationship. A Data Processing Agreement governs the processing of personal data on your behalf. They're legally distinct instruments. Request a standalone DPA or a written addendum incorporating the Article 28(3) requirements—this is a non-negotiable.
Provider can't produce ISO/SOC documentation. This doesn't automatically mean their infrastructure is insecure, but it means you're relying entirely on self-assessment. Escalate to your DPO to determine whether the undocumented risk is acceptable given your data volumes and regulatory exposure.
Provider won't explain how IPs are sourced. Walk away. With multiple established providers available in the residential proxy network market, there's no reason to accept opacity on IP sourcing.
A note on compliance scope: Completing this vetting process closes your supply-chain obligation as a data controller. It doesn't replace your own LIA, RoPA entry, or data minimization policy—those are client-side obligations you own regardless of which provider you use. Think of provider vetting as necessary but not sufficient: both tracks need to be closed before your first production request goes out.
What to Document Before You Go Live
Your compliance record is what protects your organization when a regulator requests information or a data subject files a complaint.
Your Records of Processing Activities (RoPA) entry (Art. 30) for proxy-based data collection must include: processing purpose, categories of data (IP addresses, product data, page content), recipients (internal teams, third-party analytics platforms), retention period (a specific timeframe, not "as needed"), and transfer mechanisms if data is processed outside the EEA.
Your LIA document captures the three-step analysis before any processing begins. Here's the minimum structure each section needs to contain:
This doesn't need to be elaborate—a two-page internal document that honestly addresses each step is more defensible than a polished 20-page document that doesn't. The CNIL's January 2026 guidance makes clear that supervisory authorities evaluate the substance of the analysis, not its presentation.
Your data flow diagram should trace: where proxy traffic originates, which provider infrastructure it passes through, where collected data lands (databases, analytics platforms, data warehouses), and who has access at each stage.
Breach response readiness: Under GDPR Article 33, if your provider suffers a breach affecting your processing, you have 72 hours from becoming aware to notify your supervisory authority. Your Data Processing Agreement must require the provider to notify you within 24–48 hours of any incident so you have time to assess scope and prepare your notification. Without that clause explicitly in the agreement, you're entirely dependent on your provider's disclosure timeline—which may not align with your legal clock.
Your Next Three Actions
Immediately: Check whether you have an executed Data Processing Agreement with your current proxy provider. If not, this is your highest-priority action—operating without one when personal data is being processed is a straightforward GDPR Article 28 violation, and it's the first thing a Data Protection Authority will look for.
This month: Complete a Legitimate Interests Assessment for each active use case involving proxies. Use the table above as your structure. The EDPB's Guidelines 1/2024 and CNIL's January 2026 web scraping guidance are the primary references for the balancing test.
Quarterly: Review your provider's compliance status. Certifications expire. Sub-processor lists change. Per EDPB Opinion 22/2024, signing a DPA once isn't sufficient—ongoing controller verification is a documented obligation.
Try Proxy001 — and run your compliance review in parallel.
Proxy001 provides residential proxies across 100M+ IPs in 200+ regions, covering rotating residential, static residential, ISP, and mobile proxy types. The network integrates with Python, Node.js, Puppeteer, Selenium, and most major scraping frameworks via both IP whitelist and credential-based authentication.
The free trial—no credit card required—lets you validate technical fit against your actual infrastructure before any purchase decision. If you're figuring out how to set up residential proxy infrastructure for a new use case, or migrating from a provider with opaque IP sourcing, use the trial window to simultaneously run the technical validation and request Data Processing Agreement documentation from the Proxy001 team. Getting both tracks right before go-live is the only approach that holds up when an auditor asks questions.











 English
English
 繁體中文
繁體中文
 Deutsch
Deutsch
 Français
Français
 Español
Español
 日本語
日本語
 한국어
한국어
 Português
Português