Digital ad fraud cost advertisers an estimated $41.4 billion globally in 2025, according to Spider Labs' annual ad fraud report — and that figure has been climbing year over year. A significant portion of that loss comes from fraudsters serving fake impressions, cloaking ad creatives, and violating geo-targeting rules in ways that are invisible to advertisers checking from a single IP address.
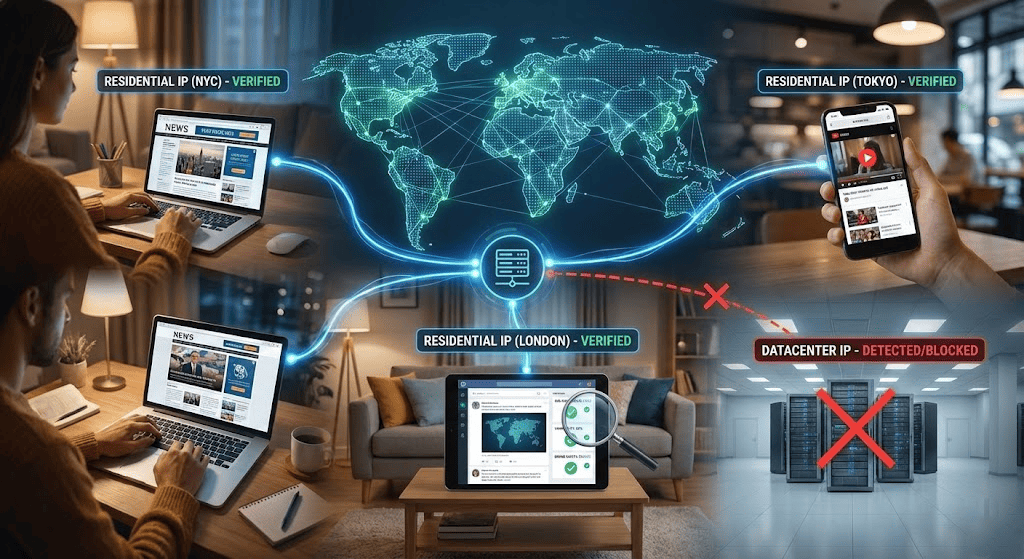
Ad verification exists to catch exactly these problems. But here's the catch: if you verify ads from your office network or a datacenter IP, ad networks and fraudsters can detect verification traffic and serve clean, compliant creatives — while continuing to serve manipulated ads to real users. Residential proxies solve this by letting you see ads exactly as consumers see them, from real ISP-assigned IP addresses in the locations where your campaigns run.
Having run geo-targeted verification campaigns across 15+ markets, one thing became clear early: the gap between what your ad platform dashboard reports and what real users actually see can be surprisingly wide — and that gap only becomes visible when you check from IPs that look like real consumers. This guide walks through the complete workflow: what to verify, how to configure residential proxies for the job, and how to integrate them with both third-party platforms and custom scripts.
What Ad Verification Actually Checks
Before configuring anything, you need to know exactly what you're verifying. Ad verification covers five distinct dimensions, and each one determines how you'll set up your proxy infrastructure.
Placement accuracy confirms that your ads appear on the publishers and page positions specified in your media buy. A campaign purchased to run on premium news sites shouldn't be rendering on low-quality content farms — but without verification from diverse IPs, you may never discover the discrepancy.
Geo-targeting compliance checks whether location-targeted campaigns actually serve only in the intended regions. If you're running a campaign targeting New York City, you need to verify from NYC residential IPs that the creative renders correctly there — and verify from outside NYC that it doesn't render where it shouldn't.
Brand safety ensures your ads aren't appearing alongside harmful, offensive, or non-compliant content. This matters especially for regulated industries (alcohol, pharmaceuticals, financial services) where placement next to certain content types can create legal exposure.
Viewability measures whether ads meet the IAB/MRC standard: at least 50% of pixels visible in the browser viewport for a minimum of one continuous second for display ads (two seconds for video). Verifying viewability from multiple geographic endpoints reveals whether your placements actually have a chance of being seen, or if they're buried below the fold on low-engagement pages.
Fraud detection identifies non-human traffic patterns — click fraud, impression fraud, cloaking (where fraudsters show clean content to known verification IPs but serve different content to regular users), and domain spoofing. This is where residential proxies are most critical, because fraudsters actively fingerprint datacenter IP ranges and adjust their behavior when they detect verification traffic.
Each of these dimensions requires you to access ad placements from IP addresses that look like real consumers. That's the core reason residential proxies are the infrastructure choice for ad verification, not an optional upgrade.
Why Residential Proxies — Not Datacenter Proxies — Are Essential
The distinction between residential proxies and datacenter proxies matters more for ad verification than for almost any other proxy use case. Here's why.
Datacenter proxies route traffic through IPs assigned to hosting providers and cloud infrastructure. Ad networks, publishers, and sophisticated fraudsters maintain databases of known datacenter IP ranges (many are publicly documented in ASN registries). When verification traffic arrives from a datacenter IP, three things can happen: the ad platform may serve different content, the publisher's anti-bot system may block the request entirely, or a cloaking operation may detect the non-residential IP and switch to serving compliant creatives — hiding the fraud you're trying to catch.
Residential proxies use IP addresses assigned by real Internet Service Providers to household devices. To the ad server, a request from a residential proxy is indistinguishable from a regular consumer browsing from home. This means you see exactly what an actual user would see: the real creative, the actual placement, the true geo-targeting behavior.
Beyond authenticity, ad verification places four specific technical demands on proxy infrastructure:
Geo-targeting precision. Country-level targeting is insufficient for most verification tasks. If your campaign targets specific metro areas, you need city-level or ASN-level proxy selection to verify from the exact network environments your ads are supposed to reach. Look for providers that offer sub-country targeting — at minimum, state and city.
IP rotation. Anti-bot systems track request patterns by IP. Sending repeated verification requests from the same residential IP will eventually trigger rate limits or behavioral blocks. Rotating proxies assign a new IP per request (or per configurable interval), letting you simulate diverse users and avoid detection.
Session persistence. Not every verification task benefits from rotation. When you're tracing a full ad click-through funnel — from impression to landing page to conversion event — you need the same IP maintained throughout the journey. This is what sticky sessions provide, typically configurable from a few minutes up to 30–60 minutes depending on the provider.
Protocol support. HTTP and HTTPS proxies handle standard web ad verification. For more complex scenarios — verifying in-app ads, testing VAST/VPAID video creatives, or routing traffic through custom toolchains — SOCKS5 support provides the flexibility to proxy at the transport layer rather than the application layer.
That said, residential proxies come with trade-offs worth factoring into your planning. They cost significantly more per GB than datacenter alternatives — generally $3–8/GB depending on provider and volume (though some providers offer lower rates at scale), compared to $0.1–0.5/GB for datacenter proxies. Latency is higher because traffic routes through real ISP infrastructure rather than optimized datacenter paths, which means page loads during verification take noticeably longer. And city-level geo-accuracy isn't always exact; we've seen residential IPs register to a neighboring city in geolocation databases, which is why the connection verification step later in this guide is non-negotiable before running production checks. For ad verification, these trade-offs are worth accepting — the authenticity advantage outweighs the cost and speed penalty — but you should budget and schedule accordingly.
ISP proxies (static residential) and mobile proxies can supplement your setup for specific edge cases — ISP proxies when you need a stable IP that still appears residential, mobile proxies when verifying mobile carrier-specific ad targeting. But for the core ad verification workflow, rotating residential proxies are the primary tool.
Choose the Right Proxy Provider
Selecting a proxy provider for ad verification isn't the same as selecting one for general web scraping. The verification use case has specific requirements that narrow the field.
Geographic coverage depth. Your provider must offer granular targeting in every region where your campaigns run. Country-level coverage is table stakes; city-level or ASN-level targeting is what actually matters for verifying localized campaigns. Check whether the provider's geo-targeting is based on IP geolocation databases or self-reported metadata — the former is more reliable for verification purposes.
IP pool size and freshness. Fraudsters and anti-bot systems flag IPs that appear repeatedly in verification-like patterns. A large, continuously refreshing IP pool reduces the chance of hitting stale or flagged addresses. Providers that add thousands of new IPs daily offer better rotation quality than those with static pools.
Rotation and session control. You need a provider that supports both automatic rotation (new IP per request) and sticky sessions (same IP held for a configurable duration) through a single endpoint — not one that forces you into separate products for each mode. The ability to switch between modes via a simple parameter change (such as a session ID in the proxy username) streamlines your workflow significantly.
Integration support. Ad verification workflows often run through automated tools — headless browsers (Puppeteer, Selenium, Playwright), custom Python scripts, or third-party platforms. Your provider should support standard HTTP/HTTPS and SOCKS5 proxy protocols and offer clear documentation for integration with common automation frameworks.
Pricing model. Residential proxies are typically priced per GB of bandwidth consumed. Ad verification is moderately bandwidth-intensive because you're loading full page renders (including media assets) to verify placements. Compare cost per GB across providers, but also check for hidden costs — some charge premiums for specific geos, session types, or concurrent connection limits.
For large-scale verification campaigns that span multiple regions, Proxy001 offers a configuration that aligns well with these requirements: 200+ regions with city-level geo-targeting, both automatic rotation and sticky sessions (up to 60 minutes), HTTP/HTTPS/SOCKS5 protocol support, unlimited concurrency, and residential proxy pricing starting at $0.7/GB. The provider also publishes integration examples for Python, Node.js, Puppeteer, and Selenium, which reduces setup friction for automated verification pipelines.
Step-by-Step: Setting Up Residential Proxies for Ad Verification
With a provider selected, here's how to configure and execute a complete verification workflow.
Step 1: Define Your Verification Scope
Start by documenting what you're checking and where:
Verification dimensions. Refer back to the five dimensions above — placement accuracy, geo-compliance, brand safety, viewability, and fraud. Not every campaign needs all five. A brand safety audit requires different proxy configurations than a geo-targeting compliance check.
Target regions. List every city, state, or country where your campaigns are active. Each becomes a proxy endpoint you'll need to configure.
Device and browser profiles. Ads render differently across desktop and mobile. If your campaigns target both, your verification setup should emulate both environments through user-agent strings and viewport configurations.
Frequency. Decide whether this is a one-time audit, a weekly spot-check, or continuous monitoring. One-time audits can run manually; continuous monitoring requires automated scripts with scheduled execution.
Step 2: Configure Proxy Endpoints
After registering with your provider, you'll receive connection credentials — typically a proxy gateway hostname, port, username, and password. Most residential proxy providers use a gateway model where a single endpoint handles rotation and geo-targeting through parameter modifications.
Set geo-targeting. Providers generally allow you to specify country, state, or city either through the proxy username string or via a separate API parameter. For example, a username format like user-country-us-city-newyork would route traffic through New York residential IPs.
Choose your rotation mode. For each verification task, select the appropriate proxy behavior:
Placement audits and fraud spot-checks → Use rotating mode (new IP per request). This simulates multiple unique users and covers more ground per verification run.
Click-through funnel verification → Use sticky sessions (same IP for 5–30 minutes). The ad server needs to see a consistent "user" progressing from impression to landing page.
Continuous monitoring → Use rotating mode on scheduled intervals (e.g., every 15 minutes), with enough delay between requests to avoid triggering rate limits.
Verify the proxy connection. Before running any verification, confirm that your proxy is working and geo-targeting correctly. Make a simple request to an IP geolocation service (such as ipinfo.io/json) through the proxy and confirm the returned location matches your target:
import requests
proxy_url = "http://user-country-us-city-newyork:password@gateway.provider.com:port"
proxies = {"http": proxy_url, "https": proxy_url}
response = requests.get("https://ipinfo.io/json", proxies=proxies, timeout=10)
print(response.json())
# Verify: "city" should show "New York", "org" should show a residential ISPIf the returned location doesn't match, check your geo-targeting parameter format against the provider's documentation — syntax errors are the most common cause.
Step 3: Integrate with Your Verification Tool
The integration method depends on your verification approach. There are three practical paths:
Option A: Cross-referencing third-party ad verification platforms. If you use platforms like DoubleVerify, Integral Ad Science (IAS), or MOAT, these tools run their own crawling infrastructure and don't typically accept external proxy configurations for their core scanning. Where residential proxies add value alongside these platforms is in running your own independent spot-checks to validate the platform's reports — or to verify placements in geo-regions where the platform's coverage may be limited. Use the same headless browser approach from Option B below to run your own verification, then compare your screenshots and placement data against the platform's dashboard. This cross-referencing catches discrepancies that either system alone might miss: cases where the platform reports a clean placement but your independent check from a different residential IP reveals a different creative or geo-targeting violation.
Option B: Headless browser automation. For full-page verification — where you need to render the ad creative, check viewability, and capture screenshots — Puppeteer or Playwright with a residential proxy gives you the most control:
// Puppeteer example (Node.js)
// npm install puppeteer
const puppeteer = require('puppeteer');
(async () => {
const browser = await puppeteer.launch({
args: ['--proxy-server=gateway.provider.com:port']
});
const page = await browser.newPage();
// Authenticate with the proxy
await page.authenticate({
username: 'user-country-us-city-chicago',
password: 'your_password'
});
// Set a realistic user-agent
await page.setUserAgent(
'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36'
);
// Navigate to the publisher page where your ad should appear
await page.goto('https://publisher-site.com/article', {
waitUntil: 'networkidle2',
timeout: 30000
});
// Capture a screenshot for visual verification
await page.screenshot({ path: 'verification-chicago.png', fullPage: true });
// Check for specific ad elements in the DOM
const adPresent = await page.$('div[id*="ad-slot"]');
console.log('Ad element found:', !!adPresent);
await browser.close();
})();Option C: Browser extension for manual spot-checks. For quick, non-automated verification — such as a media buyer manually checking placements — a proxy management extension like SwitchyOmega (Chrome) lets you route browser traffic through residential proxies and visually inspect ad placements across different regions. This is useful for ad-hoc investigations but doesn't scale for ongoing monitoring.
Step 4: Run Verification and Collect Data
Execute your verification across every target region. For each location, document:
Which ad creative rendered (capture screenshots or save HTML snapshots)
The landing page URL the ad links to (check for redirect chains)
Whether the ad appeared in the expected placement position
Whether the ad was absent in regions where it shouldn't appear
Any unexpected behavior: different creatives than expected, redirects to unfamiliar domains, or ads appearing alongside non-compliant content
If you're running automated verification, structure your output as a data file (CSV or JSON) with columns for target region, timestamp, ad presence (boolean), creative ID or screenshot hash, landing page URL, and any anomaly flags.
Step 5: Analyze Results and Act
Compare your verification data against the campaign's intended configuration:
Geo-mismatches (ad serving outside target regions, or absent within them) should be escalated to your DSP or ad ops team immediately — this can indicate misconfiguration or publisher-side fraud.
Creative discrepancies (different ads than what was approved rendering on certain publishers) may signal unauthorized creative swaps or cloaking.
Suspicious redirect chains (ads that redirect through multiple intermediary domains before reaching the landing page) are a common indicator of click fraud or affiliate fraud schemes.
Viewability failures (ads consistently rendering below the fold or in non-viewable positions on specific publishers) warrant renegotiating placement terms or adding those publishers to a blocklist.
Feed your findings back into your campaign management workflow: update publisher allowlists and blocklists, adjust geo-targeting settings, and flag fraud patterns for deeper investigation.
Rotation Strategy: When to Rotate vs. When to Stick
Getting the rotation strategy wrong can either waste bandwidth (unnecessary IP changes during a session that needs continuity) or trigger detection (reusing the same IP too many times on a single target). We initially assumed rotating on every request was always the safest approach, but found that some ad platforms interpret rapid IP switching from the same session fingerprint as bot behavior — which defeats the purpose entirely. The right choice depends on the specific verification task.
For spot-checking ad placements across multiple cities, use rotating proxies with a new IP per request. You're trying to see how ads render for diverse users, so IP diversity is the priority.
For detecting cloaking or geo-masking fraud, use rotating proxies at high frequency. Fraudsters who serve different content based on IP reputation can only be caught by hitting the same placement from many different residential IPs and comparing results.
For user journey or funnel QA — verifying that a click-through path works correctly from ad impression through landing page to conversion — use sticky sessions held for 5–30 minutes. The ad server and landing page need to see a consistent "user" progressing through the funnel, and IP changes mid-journey can break session tracking or trigger re-authentication.
For continuous monitoring with alerting, rotate IPs on a scheduled interval (e.g., a new IP every 15–30 minutes) rather than every request. This balances detection avoidance with bandwidth efficiency.
Troubleshooting Common Issues
Even with correct configuration, ad verification through proxies can hit friction — and some of these issues are deceptively hard to diagnose. Early on, we spent hours debugging what we thought was a proxy authentication failure, only to discover the issue was a truncated city name in the geo-targeting parameter. Here are the most common issues and how to resolve them.
Proxy requests getting blocked by the target site. If a publisher's anti-bot system blocks your requests, first check your request headers — a missing or obviously synthetic user-agent string is the most frequent cause. Ensure your user-agent matches a real browser. Next, reduce request frequency; hitting the same publisher too rapidly from rotating IPs can trigger rate-based blocks even when individual IPs are clean. If blocks persist, try a different IP pool region or switch from HTTP to SOCKS5 to change the traffic fingerprint.
Verification results inconsistent across runs. If the same verification check returns different results on consecutive runs, the most likely cause is cached content. Clear cookies and local storage between requests (or use incognito contexts in headless browsers). Also confirm that your geo-targeting is precise enough — a country-level proxy may route through different cities on different requests, which can affect which ad creative gets served.
Sticky sessions terminating early. Each proxy provider has a maximum session duration (commonly 10–60 minutes for residential proxies). If your funnel verification requires longer sessions, either break the verification into segments that fit within the session window, or proactively request a new sticky session before the current one expires and resume from the last checkpoint.
Bandwidth consumption higher than expected. Ad verification loads full web pages including images, scripts, video players, and ad creatives — all of which consume proxy bandwidth. To reduce consumption without sacrificing verification quality, configure your headless browser to block non-essential resources (fonts, tracking pixels, third-party analytics scripts) while keeping ad-related resources loading normally. Alternatively, reduce the number of full-page renders by doing lightweight HTTP checks first and reserving full renders for placements that show anomalies.
Proxy authentication failures with third-party tools. Double-check the authentication method. Some tools expect proxy credentials in the URL (http://user:pass@host:port), others require separate authentication headers or IP whitelisting. Confirm which method your provider and your tool each support, and match them.
Compliance and Ethical Considerations
Ad verification is a legitimate and widely practiced business activity — but it still requires attention to compliance.
Proxy sourcing ethics. Confirm that your proxy provider sources its residential IPs through opt-in programs where device owners have consented to share their bandwidth. Reputable providers publish their sourcing policies; avoid providers that can't or won't disclose how they obtain residential IPs. Using proxies sourced without user consent creates legal risk under data protection regulations and undermines the credibility of your verification findings. Also review the provider's logging policy — a verification-grade provider should clearly state what connection data they log, how long they retain it, and make their privacy policy easily accessible. If a provider is vague about logging practices, that's a red flag for both compliance and operational security.
Platform terms of service. While ad verification is a recognized and accepted industry practice, some ad platforms have specific terms around automated access. Review the ToS of any platform you're verifying against, particularly around automated crawling rates and data collection. When in doubt, keep request frequencies moderate and use verification methods that mimic natural browsing behavior rather than high-speed crawling.
Data handling. Verification processes generate data — screenshots, HTML snapshots, redirect chain logs, and ad creative captures. Some of this data may contain personally identifiable information (such as dynamically inserted location data in ad creatives). Ensure your data storage and retention practices comply with GDPR, CCPA, and other applicable privacy regulations, especially when verifying campaigns that run in jurisdictions with strict data protection rules.
Proportionality. Your verification traffic should be proportional to your legitimate need. Running thousands of requests per minute against a single publisher goes beyond verification and may impact the publisher's infrastructure. Keep request rates reasonable and distributed across your target publishers.
Conclusion
The complete workflow for ad verification with residential proxies follows a clear sequence: define what you're verifying and where, select a proxy provider with the geo-coverage and session control your campaigns require, configure endpoints with the correct rotation strategy per task type, integrate with your chosen verification tool, run checks across all target regions, and act on the findings.
Residential proxies aren't optional for serious ad verification — they're the infrastructure that makes accurate verification possible. Without them, you're checking ads through a lens that fraudsters can detect and manipulate.
Last updated: February 2026. This guide is based on ad verification workflows tested across US, EU, and APAC markets using multiple residential proxy providers throughout late 2025. Proxy configurations, code examples, and troubleshooting steps reflect current provider implementations and may change as providers update their APIs. We plan to review and update this guide quarterly.
Disclosure: Proxy001 is referenced in this article as a provider option. Our recommendations are based on documented feature sets and publicly available pricing. Readers should evaluate any provider against their own requirements before purchasing.
Start verifying your campaigns with confidence. Proxy001 provides residential proxies across 200+ regions with city-level geo-targeting, flexible rotation control (automatic rotation and sticky sessions up to 60 minutes), full HTTP/HTTPS/SOCKS5 protocol support, and unlimited concurrency — all starting at $0.7/GB. Integration examples are available for Python, Node.js, Puppeteer, and Selenium, so you can build your verification pipeline and start running checks the same day. Get started at proxy001.com →











 English
English
 繁體中文
繁體中文
 Deutsch
Deutsch
 Français
Français
 Español
Español
 日本語
日本語
 한국어
한국어
 Português
Português